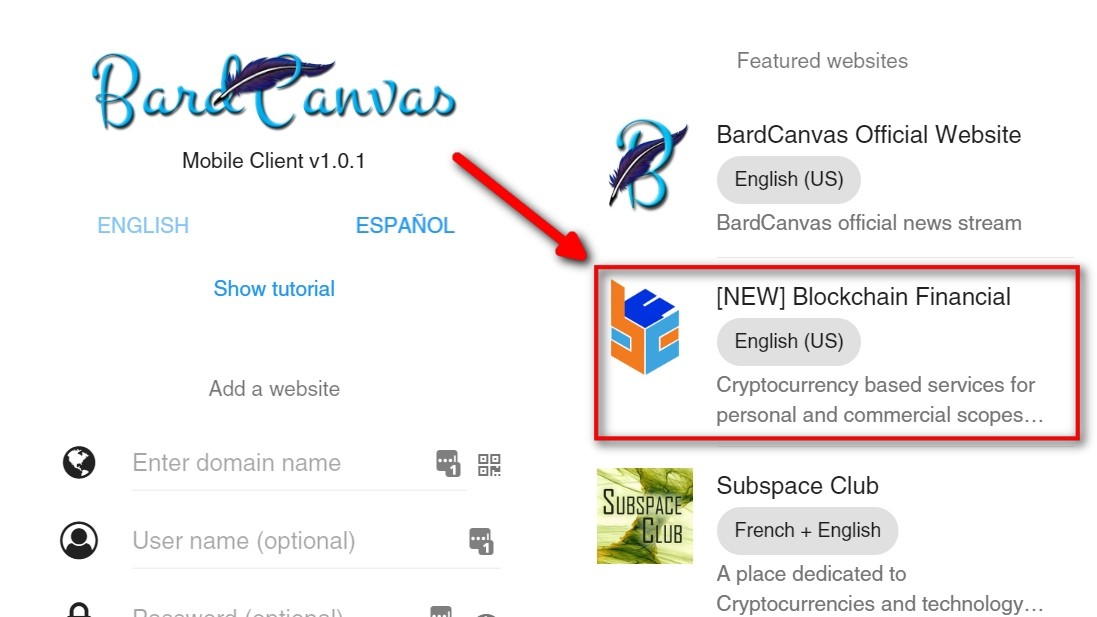
On Saturday, December 12th, I started receiving notifications about a user attempting to withdraw funds from different wallets. Then I checked all systems and saw that he already withdrew a couple hundred dollars worth of some coins, and he was trying to withdraw more, thinking the wallets were full and ready for depletion, but he didn't count on a failsafe put for this kind of events.
Stolen coins and amounts are:
| Coin | Amount | Refunded | Remaining |
| Bitcoin | 0.00706135 | All | 0 |
| Dogecoin | 2,859.13478043 | All | 0 |
| Litecoin | 0.069969 | All | 0 |
| Pandacoin | 4,690,363 | All | 0 |
| Trollcoin | 21,200.03 | All | 0 |
I'm the one to blame, and only me
I'm posting this report from my personal account because it was because of an error I made in the logic of one of the validation steps for the exchange ops, this user was able to post trades in invalid amounts, then cancel the orders while getting huge balances ready for withdrawal.
One of the first steps I took was take a quick look at the offender account and disabled it so he couldn't do more damage. Then I disabled other accounts that seemed to help him out, then took some time to dig in all systems.
It was an exploit, not a hacking
Please note:
- This was not a break-in to steal accounts info and login using stolen credentials to withdraw funds.
- Also, it was not a vulnerability in the wallet servers. The user didn't hack into them to withdraw directly from the wallets.
- Finally, only the exchange was exploited.
The user created accounts and used the exchange to trade using invalid amounts, then used the portfolio to withdraw the funds. All using a web browser.
The servers are secure, the source code is protected, all server security methods are in place and the wallets are up, running and secured.
Aftermath measures
-
Transactions reversed. All transactions generated by the bogus trades in the exchange were reversed, so a couple of valid users that had open orders taken by the offender were left with minimal or zero damage.
-
Orders removed. The orders used by the offender were left in the exchange but in a way it won't affect the rest of the exchange ops.
-
The flaw in the code has been fixed. I tried to replicate the offender's steps and I wasn't able to get away with it after the changes.
- The method used to warn admins in dangerous situations has been improved.
-
Withdrawal timing restrictions were added. No more than one withdrawal per coin per user can be requested every 10 minutes. Users with higher account levels will wait only one minute.
- Audit reports are a work in progress. I'm finishing a reporting utility I left behind that will generate audit reports, so it takes me or anyone else attending emergencies less time to react in the future.
Next steps
At the moment of writing this article, affected coin balances are obviously in red. Bringing them back to black requires two things to be done:
-
Purchase the stolen coins and deposit them so wallets don't send withdrawal errors if someone wants to take some out.
- Make amendments to the offender accounts so they don't mess up with the global balances once the audit reports are out.
The previous steps will be taken within the next weeks. I'll update this document and send notifications through all BCF social channels.
For security reasons, I can't disclose information or the details of the offending accounts, but if you want full details or want to take look at the proof I gathered, please, don't hesitate on asking through the BCF contact form. I'll personally attend these requests.
If you don't want to keep your assets here but you face problems withdrawing them, please use the same method to ask for help.
Thanks in advance for your patience.
Yours,
Alejandro Caballero.
Updates
- December 28, 4:18 PM - LTC have been refunded.
- February 26, 3:33 PM - Refunded amounts of the other coins.
- April 17, 8:05 PM - Refunded remaining DOGE.
- May 5th, 4:45 AM - Refunded remaining BTC.
- May 7th, 4:23 PM - Refunded remaining PND. Thanks to John Moore for being incredible helping out!
- May 17, 4:09 PM - Refunded remaining Troll.
Do you know you can set a label to A.Caballero?
 Blockchain Financial has a system that lets users stick labels to other users
as an alternative way to show their appreciation or discontent for
the contents of their posts or their attitude when commenting.
Blockchain Financial has a system that lets users stick labels to other users
as an alternative way to show their appreciation or discontent for
the contents of their posts or their attitude when commenting.
Do you want to be part of the elite? Become a valuable contributor!


 CoinMarketCap
CoinMarketCap CoinPaprika
CoinPaprika
Click here to register now!